IC Data Communications LLC Blog
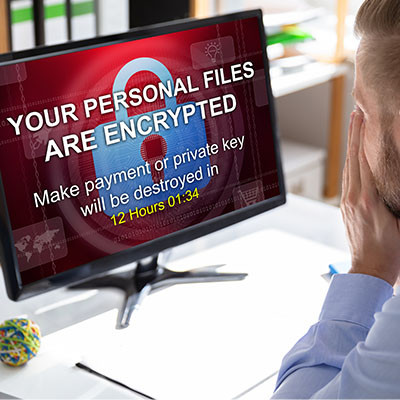
It can be too easy to look at ransomware as a business problem. After all, it attacks businesses, locking down their data for ransom, often selling it or spreading it, and sometimes altering it for the business if returning it at all. It can be too easy to overlook another impacted target in all the mess.
What happens to the people whose data a business has collected and uses?
There are many parts of running a business where you cannot be too careful, one of which is the realm of cybersecurity. Many of the preventative measures you can implement aim to keep issues from making their way to your infrastructure in the first place, which makes sense from an operational standpoint. With an endpoint detection and response solution—or EDR—you’ll take an important step toward keeping most threats off your infrastructure.
On Wednesday, April 10, 2024, Apple deemed it necessary to send a rare alert to certain users via email, spread out across 92 nations. As Apple’s website states, these threat notifications “are designed to inform and assist users who may have been individually targeted by mercenary spyware attacks.” Let’s review these attacks so we all understand this threat better.
Small businesses are presented with the challenging prospect of monitoring and policing various IT-related policies that you might have for your network infrastructure and workplace technology use. The difficulty of this notion does little to lessen its importance, however. You need to take action to protect your assets, data, and reputation from the countless threats out there, and ensuring that your employees are properly using technology is paramount to this endeavor.
Mobile malware isn’t common, but it’s growing increasingly more so. You may have heard of a malware called XLoader, which has been used to victimize people in over seven countries. This mobile threat has seen various iterations over the past several years, but you should be especially concerned these days.
For the IT administrator and the small business owner, it can be a bewildering experience when your company comes under siege from employee-induced cyberthreats; especially if you, like many other companies, have started prioritizing security training. Even if the threat is thwarted early and the effect on the business is negligible, it is important that you trust the people who have access to your organization’s digital resources. Let’s look at some of the reasons some of your staff take cybersecurity initiatives worse than others.
It’s an unfortunate fact that all businesses will inherently face some threats during their operations. That’s inescapable. From cyberattacks to natural disasters to good, old-fashioned accidents, you’re liable to face no small risk. This risk makes a process known as risk mitigation so critical for all businesses to undergo with some regularity.
Let’s review a few aspects of creating and maintaining a dependable risk mitigation strategy.
We’re hoping that you are actually reading this post to prepare yourself if your business were to face a ransomware attack, but if you are suffering from one right now, we encourage you to reach out to us immediately, whether you are a client or not. Ransomware spreads quickly, and once it has infected a system, there really isn’t much you can do to stop it. However, there are steps you need to take to come back from this gracefully.
Unsurprisingly, some of the biggest retail days of the year are some of the biggest days for scams, the entire holiday season seeing an increase in threats toward retailers and, as a result, the consumers that are just looking for that perfect gift for their loved ones. Let’s review some statistics and trends to see what insights we can glean.
With ransomware becoming one of the single most dangerous threats out there for small businesses, it’s more important than ever to know how to protect your company from its influence. Thankfully, there are measures you can take, including some very powerful ones like zero-trust policies that can thwart attempted ransomware attacks.
Countless challenges arise for businesses, ranging from supply chain disruptions and employee turnover to the unpredictable forces of natural disasters. Among these challenges, cyberattacks stand out as an inconspicuous yet highly menacing threat. In this article, we delve into the various ways cyberattacks endanger your business and provide insights on how to prepare for them effectively.
Social media scams encompass fraudulent activities and deceptive schemes that occur across various social media platforms. These scams target users on platforms like Facebook, X (formerly Twitter), LinkedIn, and numerous others, irrespective of their age or background. They exploit individuals' trust, curiosity, or lack of awareness. Social media scams manifest in various forms, and the following are some common examples.
With data security being a hot commodity with hackers, it’s no surprise that businesses want to do everything they can to protect their assets. One method for doing so is implementing a Virtual Private Network, or VPN, that can effectively obfuscate data while it’s in transit. Let’s go over some of the most valuable reasons why your business should be using a VPN.